Backup methods combine full baselines with incremental updates to balance speed and storage. They rely on strategic copy patterns and diverse storage—on-site, offsite, or cloud—for resilience and quick recovery. Guardrails like verification, testing, and cadence ensure data integrity and repeatable success. The result is a resilient, governed process that supports timely restores. Yet the specifics of implementation and governance determine how effectively recovery is actually guaranteed, prompting further examination of options and trade-offs.
What Backup Is Really Doing for You
Backup serves as the safeguard that ensures data availability and continuity, translating routine storage into reliable resilience.
The analysis frames backup as a strategic control: it gauges backup effectiveness, ensuring timely recoveries, and maintains data availability across environments.
It evaluates risk, prioritizes restoration timing, and informs governance.
Each two word discussion ideas about subtopic not relevant to other H2s: reliability planning, redundancy metrics.
Full Vs Incremental: How Every Copy Shapes Recovery
The previous discussion established that recovery readiness hinges on how data is preserved. Full copy establishes a complete baseline, enabling rapid restores but demanding storage and bandwidth. Incremental copy captures only changes, reducing footprint yet necessitating a sequence of restores. Strategic use balances speed and efficiency, clarifying recovery windows: prioritize full copies periodically, with incremental copies sustaining ongoing resilience and freedom.
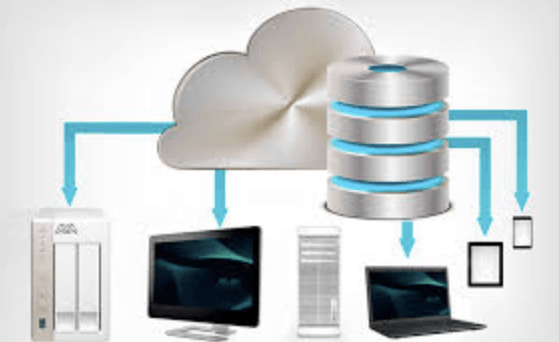
Where to Store Backups: On-Site, Offsite, and Cloud Options
On-site, offsite, and cloud storages each offer distinct benefits and trade-offs for backup strategy. The analysis compares control, cost, and accessibility: on site favors rapid restores, offsite mitigates physical risks, and offsite cloud provides scalable redundancy.
Selection blends these modes to balance resilience with agility, prioritizing data criticality, recovery objectives, and long-term flexibility. cloud storage remains a scalable option.
Guardrails That Boost Resilience: Verification, Testing, and Cadence
Guardrails that boost resilience hinge on rigorous verification, disciplined testing, and disciplined cadence. In practice, verification cadence formalizes how evidence is gathered and validated across backups, ensuring integrity without delay. Testing cadence enforces regular, repeatable exercises to reveal gaps before failure. The result is strategic resilience: clear metrics, disciplined execution, and freedom from ambiguity in recovery readiness and decision timing.
Frequently Asked Questions
What Factors Determine Optimal Backup Frequency for Different Data Sets?
Data prioritization and data diversification guide optimal backup frequency: high-priority, change-rich datasets require frequent cycles; medium Importance with moderate changes can tolerate longer intervals; low-priority, stable data favors infrequent backups, balancing risk, resources, and strategic freedom.
How Do Versioned Backups Handle Corrupted or Deleted Files?
Like a vigilant archivist, versioned backups isolate corrupted or deleted files through versioning strategies, enabling restoration from prior clean states. They support corruption detection, allowing rapid rollback while preserving historical options for strategic resilience and freedom.
What Security Considerations Protect Backup Data at Rest and in Transit?
Data encryption protects backup data at rest and in transit, while access controls limit who can view or modify it; backup integrity checks detect tampering, and data privacy measures ensure sensitive information remains restricted, supporting strategic, freedom-loving risk management.
Can Backups Recover Application-Specific Metadata and Configurations Automatically?
Ironically, yes, backups can recover application-specific metadata and configurations automatically, though it reveals foresight’s limit. It requires robust restore automation, versioning strategy, and data integrity, with encryption and access controls safeguarding backup metadata and recovery processes.
See also: Logistics Technology Trends
What Are the Costs and Trade-Offs of Long-Term Retention Policies?
Long term costs arise from storage, tooling, and governance, with retention tradeoffs balancing risk and cost. Strategic analysis notes backup frequency, data aging, and regulatory needs to optimize efficiencies while preserving freedom to restore essential history.
Conclusion
Backup strategies blend rapid full baselines with efficient incrementals, ensuring fast restores without unnecessary sprawl. An analytical lens reveals how storage choices—on-site, offsite, and cloud—shape recovery windows and resilience. Guardrails—verification, testing, and cadence—turn plans into repeatable practices. In this landscape, data integrity stands as the bedrock, and strategic orchestration of copies, locations, and checks keeps recovery outcomes predictable. Like a well-turnished toolkit, the method enables timely, governed resilience under varied risks.